When ‘ oops’ doesn’t cut it: Web giant’s capture of information using Street View vehicles just latest privacy snafu
VITO PILIECI
Sun
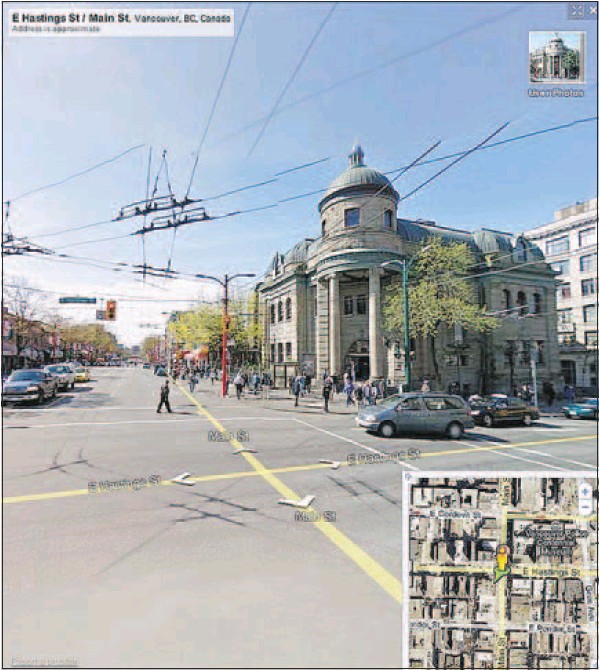
Street view in Metro Vancouver: Main and Hastings with the Carnegie Centre. Google admits that while it was mapping, it was also automatically collecting information sent over several of the networks it was scanning. GOOGLE MAPS
For a company that touts the motto “ don’t be evil” one has to wonder how Google Inc. manages to get into so much trouble. The Internet search giant can’t seem to stay onside with Canada’s privacy commissioner, falling out of favour with the watchdog repeatedly, and yet, somehow managing to skate away from each issue unscathed.
However, this latest snafu is one the company can’t easily defend.
In a puzzling turn of events, Google has been caught using its controversial camera-laden Street View vehicles to do more than just snap pictures. It seems those same vehicles were using Wi-Fi sniffing software called Kismet, to allow Google to automatically collect information about wireless networks including whether they are encrypted.
As an added bonus, some extra software was added by a Google programmer to spice things up, capable of grabbing packets of information sent over several of the networks it was scanning.
So how much data did the company get?
Well, according to the company’s latest admission, around 600 gigabytes, the equivalent of nearly 600 movies downloaded from Apple Inc.’ s iTune store.
Bits and pieces of information have been revealed by the Internet search giant as international privacy regulators have pushed the company to come clean and explain exactly what it was doing and why it needed information about private wireless networks.
You know, the ones behind locked doors, inside people’s houses.
While stopping the company from collecting data is easy — just turn on the encryption on your router — there is no way to stop the company from collecting personal information that identifies your home wireless network.
That personal identifying information beams outside the walls of your home, which is why Google is able to collect it.
The 600 GB of personal data collected could prove to be a privacy snafu of epic proportions once the data are sifted through by authorities.
The packets taken off of private wireless networks could include things like credit card numbers, bank account data, texts from personal chat sessions, e-mail or personal photos.
Google has stated publicly the information wasn’t shared outside of Google and will be turned over to international privacy officials. The company has also created an independent body to conduct an internal review of its privacy policies.
“ We screwed up. I’m not going to make any excuses about it” said Google co-founder Sergey Brin at a Google event in San Francisco on May 19. “ We do have a lot of internal controls in place but obviously they didn’t prevent this error from occurring.”
While the cataloguing of personal network identification information was intentional, capturing data on those networks was not, or so the company says.
Google also said it was not targeting any particular information.
The company said it was unaware of this rogue software that was running in tandem with Kismet. The software somehow found its way onto almost every Street View vehicle in more than 30 countries.
The oversight poses the question, if this piece of software snuck through the cracks, what else is going on that Google doesn’t know about, and why in the world would Google need to map people’s private wireless networks in the first place?
Jennifer Stoddart, the privacy commissioner of Canada, quickly issued a statement after Google’s Wi-Fi goof was recently revealed.
“ We have a number of questions about how this collection could have happened and about the impact on people’s privacy,” said Stoddart, in a release on June 1. “ We are very concerned about the privacy implications stemming from Google’s confirmation that it had been capturing Wi-Fi data in neighbourhoods across Canada.”
Kismet is used primarily by network administrators. It is also used by hackers who partake in a process called “ War Driving”.
War Driving, a term used by both the security and hacking community, sees people drive around a neighbourhood looking for a network that has been left open, often so they can hop on and use the Internet for free.
According to a spokeswoman from Google, the company was undertaking the collection initiative in order to improve Google’s geolocation services, an alternative to Global Position Services ( GPS).
These services use the unique ID of a wireless router to locate a person’s home on a map.
Think of it like an address that only your cellular phone can see. When someone walks by your house, your wireless network’s ID tells that person exactly where they are standing. In other words, Google aims to turn your private home network into public infrastructure. Why? Because it can. Peter Eckersley, staff technologist at Internet privacy watchdog group the Electronic Frontier Foundation, said the Google situation raises a number of interesting issues.
Eckersley said the collection of personal information from private networks was inexcusable, especially for a company with as many resources as Google. “ This is clearly troubling,” he said. He condemned Google for capturing personal information on various wireless networks. However, he stopped short of saying Google should be barred from its Wi-Fi mapping initiative, saying the technology could be useful if the privacy concerns could be addressed.
“ There are some privacy concerns about these databases that Google are building. But it’s not clear that those concerns are enough to prohibit the collection of that data in the first place,” said Eckersley.
So, the issue basically boils down to Google’s initiative to create an alternative to GPS by piggybacking on private Wi-Fi networks.
Doing so allowed them to “ accidentally” capture private data moving across those networks, which isn’t surprising given how many people are running wireless home networks with no encryption. To put it more simply, what Google is doing is like having a person stop by your house to fill up a bucket with water because you left the sprinkler on in the front yard. You paid for that water, just like you pay for your Wi-Fi and router. That is privately owned equipment. Still, the question about whether Google should be able to derive a benefit and turn a profit by piggybacking a service on private equipment is an interesting one, and one that needs to be answered by government quickly.
© Copyright (c) The Vancouver Sun
